Valuing consumer privacy
The topic of consumer data privacy needs no introduction. We have hit a stage in technology development where ensuring that users data stays in user control is both critical and necessary.
Consumer opt-in does not work
A ton of business logic is built on the notion that data can be collected via a single policy acceptance—this makes changes hard for service providers.
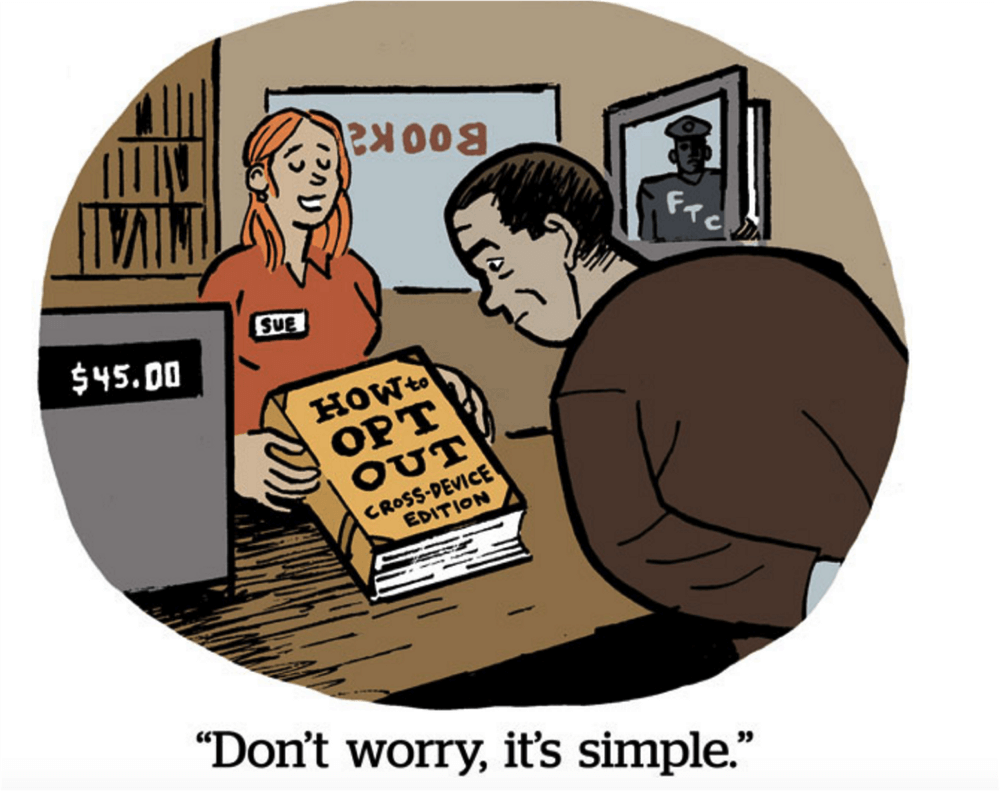
Currently, the onus is on the user to opt-out of services, while providers get away by publishing privacy notices that consumers fail to fully read or comprehend. Users also do not realize that personal data like their IP-address, their exact GEO location, their cookie-ids, and their smartphone advertising IDs can all lead to them getting tracked via other 3rd party providers. Without users fully understanding how data is collected, secured, enhanced, processed, and shared, consumers will continue to remain under surveillance.
Service providers get away with any shady practices so far as users can opt out because current compliance laws are OK with broad user opt-in so far as users accepted a broad notice, and have the right to opt-out. However, what lies inside these privacy policies is hard for a common user to fully comprehend.
Current government oversight and regulation is helping to solve the issue, but there is still a gaping hole in terms of consumer protection. Popular platforms, like Facebook, get away with mass breaches by paying fines that have no impact on their business while monetizing user data at scale. The user gets but a bitter taste of their lives publicly paraded. The day U.S. Congress announced a fine of $5B to Facebook, its market cap had already made up the penalties by adding more than $5B in their market cap—essentially the market was expecting a harsher punishment.
Issues with privacy by trust
Does Privacy by trust work at all? Does it make sense to let providers capture user trust when, in reality, the users almost always end up on the wrong end of the bargain?
Let’s take an example; a company called Liveramp provides a service called Identitylink. Identitylink allows any service provider to get consumer data about any user by providing their ID (cookie-id on their browser or advertising-id on a consumer’s smartphone) and get many more attributes about this customer.
There are a couple issues worth noting; a) the service provider is breaching consumer trust by using such a service because the consumer clearly did not know that their digital ID would be used for such a purpose and b) the consumer likely does not even know that their existing personal data elsewhere was already linked to a digital identifier and made available for a price. The fact that Liveramp says that they match the ID to consumer data in a privacy compliant manner is really good privacy humor!
It also turns out one of the top providers of data is a company called Experian; the same company that our credit card providers entrust to process our credit card data.
Likewise, when Google merged seventy privacy policies without fully explaining to the user what was going on, they essentially shared your data from one service with the other and vice-versa. This enabled them full access of our lives without scrutiny across all of their services unhindered. It is not clear how Google got away with Antitrust right there, but they did. Google, for what it’s worth, breached consumer trust because it was bait-n-switch at billion user scale and created a monopoly that has been allowed to run without any state intervention. Exactly the opposite of #donoevil; killing competition, jobs, and filling shareholder pockets.
The fact that Liveramp and others openly trade consumer data and map them to digital identifiers such as IP-address’, cookie-ids, advertising-ids, etc. makes it hard to think how any consumer can trust their service provider unless 10-page privacy policies are to be read by all.
And similarly, when providers like Google are allowed to swap privacy policies at their convenience, it is unclear how the consumer has any control with the current regulations that enforce consumer to trust an enterprise first.
The consumer always loses making ‘Privacy by Trust’ hard to defend.
Enter privacy by design
Privacy by design allows users to be in absolute control of their data at all times. Under no instance will a privacy by design technology stack provider hold a user’s personal data, unless mandated by law or required for the product to work. And when such data is collected, under no circumstances can that data be shared, or processed for anything but the purposes it was collected for—to provide that specific service. Ideally, consumer data at any provider should get locked via a private key consumer owns; this will automatically prevent data to be leaked without user permission. Sadly, this makes for non trivial changes; but baby steps are possible.

Many decentralized applications have started to allow data to be held at the user end and still create viable technology at scale. A clear example is the Brave Shields product that ensures that all websites are served by the Brave browser with 3rd party tracking off by default, and then lets the user choose if they proactively want to increase exposure to the provider proactively.
While the changes do provide privacy, the provider will need to adapt to avoid losing revenue in the process as these steps may impact monetization of the website or the app.
We hope the providers respect users privacy defaults while entering the new world and support monetization for providers with privacy defaults set in. See our post about the device edge providing interesting ways to support computing with a notion of privacy by design.
From a consumer point of view, privacy by default always wins. There is, however, work left to be done to change the existing ecosystem to adapt to a future where only data that is absolutely needed is collected and providers pay fines that prevent them from operating if they breach consumer trust.
Blotout privacy principles
Respecting consumers personal data privacy does create new challenges for website and app providers. Blotout is creating services and tools developed at the edge with a privacy by design approach to meet some of these challenges.
You can read our last post in this series of articles that explains the possibilities about computing at the edge while keeping user privacy intact.
Follow us here.
Thanks.
The Blotout team.