The world’s first client computed, privacy by design, product analytics SDK for application and web developers.
Recommended pre-reading
- Privacy has muscle at the device edge
- Privacy by trust vs. Privacy by design
- Kiss: making privacy by design easy
Next turn of technology
The next generation of internet and technology is not about new functionality, but mostly about how to re-invent existing technology for a privacy centric world. The same toolkits and the same workflow, but adjusted for privacy by design where we respect the notion of someone’s private data. And we are much closer to that reality than we think.
We have to change; not just for our sake but for the sake of our children. That change needs to happen now!
The future is First Party
A picture is worth a thousand words. The largest Tech companies are surprisingly forcing changes for our own good.
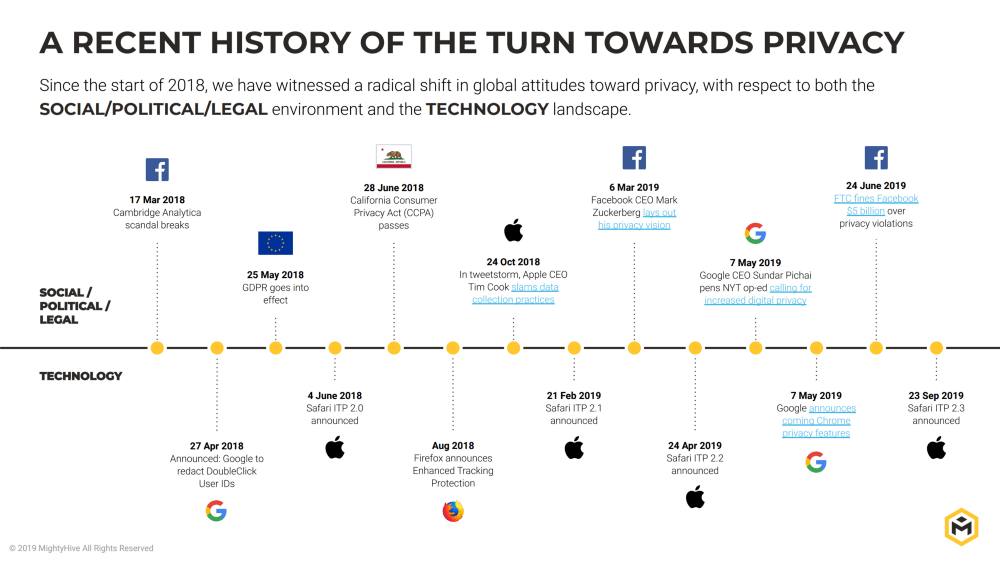
If this trend continues, all systems will move to first party data and eliminating companies in the middle transacting on data vs. the relationship of the consumer and the Enterprise.
Privacy by design and simplicity
Recently we wrote an article comparing Privacy by Design to Privacy by Trust to help create an understanding on why current compliance laws are not enough because as they rely on corporate trust diminishing the true privacy controls of the consumer. As we know, consumers have no chance of lobbying and winning. Most developers are also consumers that care for their own privacy, and hence becoming the necessary change agents. So, developers who care about data privacy now have a choice, and are the industry “Change Agents” who will drive true privacy for the consumer.
Simplicity for switching from the old ways to a privacy centric way, on the other hand, is a must for this change to occur. If privacy first toolkits that can enable businesses to succeed and garner consumer trust are not easy to use, change will become harder and frustrating. Read our article describing exactly the need to keep it simple.
Switching is never easy and always has a cost. The question becomes which cost is worth taking on; The cost of switching analytics platforms or the cost of trust with your consumer.—keeping humanity vs. managing greed.
Issue: Current stream of Privacy thinking
There is a ton of confusion around the difference of privacy and anonymizing data. They are, by nature, different.
The idea of collecting and anonymizing is still saying—hey enterprise, I trust you and I sincerely hope you are anonymizing me from your data collection as you collect data about how I use your app. Relationship is trust based.
The idea of privacy is saying—hey enterprise, how about I tell you how i am using your app without telling you who I am. Private by design.
The Power of Computing On-Device
Smartphones have an ever-growing and immense computing power which can easily process users data. This offers us a choice to keep data in the hands of the consumer, utilize distributed computing that lowers costs, keeps data at the edge enabling privacy by design, and deliver the same or better business and product development results. In some cases, edge computing renders results faster than cloud based computing.
To help one understand the concept, almost all of the Smartphone CPUs are at or near parity to most desktops; CPU is what is required to process data locally and the power requirements are miniscule. Smartphones connected to a network are the perfect distributed computing system that eventually can become the backbone of future computing, removing the need for a central cloud based structure.
Key Point: Power back to the Consumer
With Blotout, we are utilizing some principles where the user is always in full control of their full data. We are not pro-ad-blocking, we are pro-privacy and pro-user-power while enabling an existing ecosystem that needs re-thinking and re-tooling.
With Blotout, enterprises get Business Intelligence they need while giving complete power back to the user in terms of “do not track”.
Current technologies are simply working around data blocking technologies and skirting the laws by utilizing highly encroaching technologies with tracking via cookie sync’ing, IP address matching, “fingerprinting”, and ID based graphs. These data practices will go away as they’re not following the spirit of consumer privacy, and key stakeholders are taking action to eliminate. But…Apps and Content Creators need to be able to find a middle ground where users personal data is not compromised and unsafe in the cloud while enabling the basic ability to see how a piece of app or content is consumed.
With Blotout tech stack, when a user says I am done with the App and/or Site, the user has deleted all its ability to be tracked by the App or Site ever again. Zero ID, Zero IP, Zero Tracking and never worry about opt outs.
Blotout Analytics and Re-Engagement Suite v0.1
Today, we are announcing the launch of Blotout Analytics which is a privacy by design, edge computing Analytics software solution that allows developers to get the same level of analytics with zero ID, zero IP capture. AKA—no cookies, IDFA, GAID, IDFV, or IP collection on server.
To adhere to simplicity principles, Blotout Analytics will ensure that there is no loss of user analytics functionality; the integration and codification of Blotout analytics SDK is similar to the existing analytics providers allowing a seamless switch.
Architecturally and safety wise, Blotout is miles apart from current providers in-market. At no point are events correlated or sent with any PII; and at all points user can opt out of analytics without having to ask for erasure—there is no user associated data anywhere in Blotout. The server never keeps any user private data; and soon you can have your App or your Site interact with the user on the edge, with no idea who the user is.
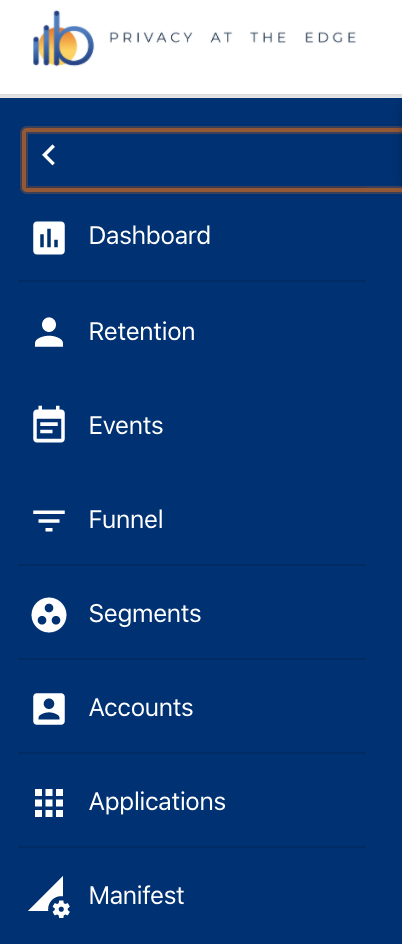
Blotout, today at launch, provides a privacy by design Android, iOS SDK and a JS SDK;
- Complete event analytics as is present with providers today
- Client Computed Funnel
- Client Computed App Segmentation
- Retention App that is Edge Smart
- A Client stored time-series DB that will eventual run ML on the Edge itself (no Privacy issues)
You will immediately see a reduction in your cost of data storage and associated server processing as these calculations are made at the edge.
However, to keep things private, events are randomly delayed; features like funnels and segments take time to build as clients compute when they are active and resources are available.
Small compromise for a privacy by design future.
On a cost/benefit side, computing power is attributed back to the user and the total cost of server processing goes down significantly. It is a good balance of getting privacy back and achieving a perfectly capable distributed computing center.
Why Analytics?
For older folks who have lived through the dot-com times, it all started with basic site analytics during the boom and continued into the era as we know “programmatic media”. One of the first applications of data collection was the ability to track user behavior on websites—soon after, advertisers and ad tech companies began utilizing this technology, somehow thinking this is the best way to engage their customers; overstepping, invading and not respecting the privacy of the consumer, nor the relationship that the publisher has with its audience.
Hence, Analytics! Start the process all over again, but let’s do it right this time around.
Analytics products are universally used, and one of the few applications where privacy is breached every microsecond. And a product where IDs and finger printable data should be required.
So, why not? Everyone should switch to Privacy by Design analytics but a lot of us will find it hard to switch; when i can track every user that have no lobbying abilities, why should i bother? Let’s not forget as developers, need to be the change we want to see in the world.
Next up v0.2: App Re-Engagement
Analytics is just the beginning; then we are going to show the world that application re-marketing (re-targeting) is perfectly possible in a no ID, no finger printable world and removes all the required hooks from app store providers.
As with all our features, re-marketing is designed with privacy in mind. When a user has downloaded and using your app, you can retarget. When they uninstall and leave, they are untraceable! It’s pretty criminal to retarget users who have left your apps on other platforms—that is a significant breach of their privacy, like it is yours too!
Unlike today, where finger prints are left with Google, Facebook, Twitter, etc. and they claim to have removed your trace, privacy by design re-targeting leaves the user alone. Once they have left your ecosystem, their ID traces are fully gone from a tracking perspective.
Our vision for Blotout
Our goal is to rebuild the stack from the bottom up. Today we’re starting with the essential analytics that drive an app based business forward. Tomorrow we focus on advanced ML Edge and Federation thinking that focus on client-based learning models.
We hope to soon prove to the developer community that privacy by design can not only compete with current privacy breaching technologies, but rather surpass them with improved efficiencies and capabilities.
Our goal at Blotout is to show that edge based computing can save humanity but also solve a critical set of issues at the edge, faster than any cloud prediction service can; at scale!
If you want to try out our solution, email us here. If you would like to invest in the future, email us here. Read more about us.
Thank you.
The Blotout team.